application of rfid security system This review paper is based on Radio Frequency Identification technology(RFID), reviewing the .
The NFC card uses NXP 215 chip, 504 bytes of memory, highly sensitive .
0 · what is the best rfid blocking method
1 · rfid technology pros and cons
2 · rfid systems for small business
3 · rfid card what is it
4 · rfid based tracking system
5 · rfid based location tracking system
6 · best rfid access control system
7 · 10 door access control system
2017 NFL playoffs schedule: Wild card schedule, matchups, dates, times . NFC first round byes: Dallas Cowboys, Atlanta Falcons. Latest NFL News. Ravens Receive A .
Radio frequency identification (RFID) is widely used in several contexts, such as logistics, supply chains, asset tracking, and health, among others, therefore drawing the attention of many researchers. This paper presents a review of the most cited topics regarding RFID ."This paper presents an interesting topic in RFID technologies application and .Feature papers represent the most advanced research with significant .Feature papers represent the most advanced research with significant .
An RFID access control system is a security management system based on radio frequency .This review paper is based on Radio Frequency Identification technology(RFID), reviewing the .
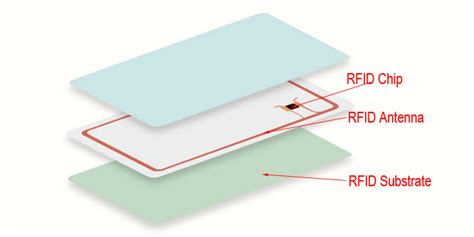
Radio frequency identification (RFID) is widely used in several contexts, such as logistics, supply chains, asset tracking, and health, among others, therefore drawing the attention of many researchers. This paper presents a review of the most cited topics regarding RFID focused on applications, security, and privacy.An RFID access control system is a security management system based on radio frequency identification technology, designed to control and manage personnel access to specific areas. The system achieves contactless access control by identifying users carrying RFID tags and is widely used in enterprises, schools, hospitals, and other locations. This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks.This review paper is based on Radio Frequency Identification technology(RFID), reviewing the security aspect of RFID and its application. RFID technology has a wide range of applications such as Logistics & Supply Chain Visibility, Race Timing, Transportation Payments, and .
This paper presents a review of the most cited topics regarding RFID focused on applications, security, and privacy. This bulletin provides an overview of RFID technologies and recommends practices for initiating, designing, implementing, and operating RFID systems in a manner that mitigates security and privacy risks. “Security issues in RFID system” presents various attacks possible on RFID devices. This section includes the attacks based on the CIA (confidentiality, integrity, and availability) properties of the RFID system.This paper presents a review of the most cited topics regarding RFID focused on applications, security, and privacy. A total of 62,685 records were downloaded from the of Science (WoS).
Abstract: Radio Frequency Identification has tremendous potential when applied to security systems. From anti-theft to physical access, the technology has been applied in numerous ways to both enhance existing systems and become the core component of brand-new ones.
what is the best rfid blocking method

rfid technology pros and cons
So to help businesses, property owners and security teams get the most out of RFID door readers, this guide aims to explain exactly how RFID door access systems works, what to look for in an RFID key lock and the best use cases for RFID doors. Radio frequency identification (RFID) is widely used in several contexts, such as logistics, supply chains, asset tracking, and health, among others, therefore drawing the attention of many researchers. This paper presents a review of the most cited topics regarding RFID focused on applications, security, and privacy.

An RFID access control system is a security management system based on radio frequency identification technology, designed to control and manage personnel access to specific areas. The system achieves contactless access control by identifying users carrying RFID tags and is widely used in enterprises, schools, hospitals, and other locations.
This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks.This review paper is based on Radio Frequency Identification technology(RFID), reviewing the security aspect of RFID and its application. RFID technology has a wide range of applications such as Logistics & Supply Chain Visibility, Race Timing, Transportation Payments, and . This paper presents a review of the most cited topics regarding RFID focused on applications, security, and privacy.
This bulletin provides an overview of RFID technologies and recommends practices for initiating, designing, implementing, and operating RFID systems in a manner that mitigates security and privacy risks. “Security issues in RFID system” presents various attacks possible on RFID devices. This section includes the attacks based on the CIA (confidentiality, integrity, and availability) properties of the RFID system.This paper presents a review of the most cited topics regarding RFID focused on applications, security, and privacy. A total of 62,685 records were downloaded from the of Science (WoS).
Abstract: Radio Frequency Identification has tremendous potential when applied to security systems. From anti-theft to physical access, the technology has been applied in numerous ways to both enhance existing systems and become the core component of brand-new ones.

rfid systems for small business
harber london leather bifold wallet with rfid protection
Use the PRESTO app for iPhone to: • Convert a physical PRESTO card to PRESTO in Apple Wallet and tap your iPhone or Apple Watch to pay for transit (not available on OC Transpo) • Load funds instantly with NFC. • Load transit .
application of rfid security system|rfid systems for small business